Table of Contents
The inclination towards online education is spiking every year. In the year 2009, it was reported by classrooms reported by students that on average, among every five individuals only one had a computer or laptop. Within the last ten years, surveys have revealed that more than 95% of school and college students have a personal computer or a laptop. Additionally, more than 90% of respondents mentioned that having a laptop is highly important to pursue their studies. Since there is a huge growth in owning personal devices, it is specifically important for individuals pursuing higher studies to be aware of online safety. As per Forbes, incidents related to data breaches and scams are also rising in the present times, with numbers shooting from 128 million in 2021 to a whopping 422 million in the year 2022. This is quite alarming and precautions must be taken from everyone’s end.
One of the best ways to improve students’ online security is by using a VPN, or virtual private network service. A VPN allows one to set up a virtual network that links persons via the internet, providing the same benefits as a physical network. This blog, ideated and written by the experts at AllAssignmentHelp will be discussing about the usage, benefits, and other points related to VPN to help students get the most out of it.
What is a VPN?
VPN stands for Virtual Private Network. When one uses the internet, his/her device is continually sharing data with other users on the web. Without realizing it, they frequently allow websites access to their real IP address revealing their exact location, browser history, OS information, device identifiers, and lots more.
A VPN functions similarly to a private tunnel, protecting his/her online activities and sensitive data. A VPN encrypts the internet connection and protects data from those who may attempt to follow or snoop on one’s online activity. In a nutshell, VPNs form a secure tunnel between one’s device (PC, Tablet, Smartphone, or Laptop) and the internet. They also protect identity and online activity from colleges, internet service providers (ISPs), and cybercriminals.
Using a VPN for students into online studying or pursue an online course is highly beneficial. Colleges around the world are offering great higher study opportunities. Suppose a student located in Sydney, Australia wishes to get enrolled in a USA-based college, using a VPN is the best option to pursue such a course from thousands of miles away and with the comfort of doing it from their house.
Read more: Understanding Cyberbullying as an Online Harassment Issue and Its Major Effects
Why do You Need to Use a VPN Service?
If you are a student and pursuing an online course, using a VPN service can be highly beneficial for a handful of reasons.
Let’s take a quick look at these below:
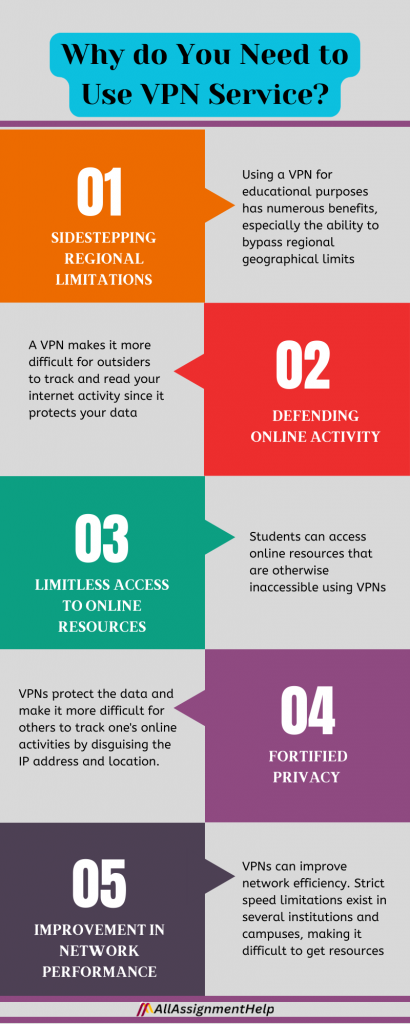
Sidestepping Regional Limitations
Using a VPN for educational purposes has numerous benefits, especially the ability to bypass regional geographical limits. Many countries have strict laws about how to use the internet. Some colleges and universities may also block access to certain websites. To browse these websites, connect to a computer in another country via a VPN. Students studying abroad will find this useful because they may require access to specific equipment in their foster country.
Say a student wants to access a website that is forbidden in the UK. They can connect to a VPN server in the United States and view the website as if they were physically present there. This is a simple and effective way to bypass local restrictions and gain access to materials that may be critical to their education.
Defending Online Activity
VPNs also protect your online activity from prying eyes. When you use a public Wi-Fi network, hackers and other third parties can view your internet activity. A VPN makes it more difficult for outsiders to track and read your internet activity since it protects your data.
VPNs mask your location and IP address, making it more difficult for observers (especially college authorities) to track your online activities. Students conducting online research will find this particularly useful because it helps them to protect their privacy and anonymity.
Limitless access to Online Resources
Students can access online resources that are otherwise inaccessible using VPNs. For example, some intellectual publications and libraries are exclusively available in specific countries. A VPN allows students to connect to a computer in that nation and have access to these resources.
Students can use VPN permission to utilize online resources that their college or school has blocked. Some businesses block access to specific websites or services for security concerns, but these restrictions can make studying more difficult for students. A VPN allows students to overcome these limits and get the materials they need for academic feat.
Suppose you are pursuing an online course in Finance and under tremendous academic pressure. It is because you have an assignment to submit as well as have to attend an online class within the next two hours for the rest of the week what would be your thoughts on this situation. Most of the students at this point either burn out or think of a way out of thinking, I wish I had someone to take my online finance class. If they have a VPN service, they can find out an online class help service from the internet and let their expert appear in the online exam without letting the college authorities know about it. Similarly, they can seek finance assignment help to get rid of the extreme pressure and have some breathing space.
Fortified privacy
Many students prioritize anonymity; VPNs provide numerous layers of security to protect their online activity. As previously said, VPNs protect the data and make it more difficult for others to track one’s online activities by disguising the IP address and location. When engaging in an internet study, anonymity can be extremely helpful.
Virtual private networks can help keep one’s ISP from monitoring internet activities. ISPs provide a security risk since they track and sell their users’ online activity to advertisements. VPNs improve both your privacy and security by prohibiting your ISP from monitoring what you do online.
Thinking I need one to help me manage my academics like appearing in an online exam scheduled in the next six hours as I am too tired. Without any worry, you can search on Google by typing Take my online exam for me and get trusted services for taking care of your exams using a VPN service.
Improvement in network performance
VPNs can improve network efficiency. Strict speed limitations exist in several institutions and campuses, making it difficult to get resources. A VPN allows students to bypass these restrictions and gain faster and more efficient access to tools. Furthermore, VPNs can improve network performance by reducing data loss and delay. Students who participate in low-delay online games or video chatting should pay close attention to this.
VPN servers are commonly scattered around the globe. Connecting to a computer physically close to your location can reduce latency and improve the overall effectiveness of your internet connection. This guarantees that your online educational experience is smooth and uninterrupted.
There are so many pros of using a trusted VPN service to get the most of your online education.
Read more: Impact of Online Classes on Traditional Learning Methods
What are The Different Technologies Behind a VPN?
A handful of technologies are used in a VPN.
Let’s take a look at those below:
Remote-access VPN
Remote-Access VPN lets each customer to establish a secure connection with remote PC networks. These clients have access to the network’s secure assets. As if they were directly connected to the network’s servers.
Site-to-site VPN
A site-to-site VPN uses a similar standard. It enables open workplaces in specific fixed locations to establish a secure connection with one another over open networks. For example, consider the Internet. It expands the organization’s network. Site-to-site VPN allows representatives to access PC assets from one location to another. The connection has been established between two VPN gateways. It exists in two different Internet networks. The exchange of PC resources between the two networks is their primary goal.
Tunneling protocols
Tunneling is the underlying mechanism for establishing a VPN. This includes the use of various encapsulation technologies and transmission protocols. This creates a safe virtual tunnel for trip internetworking. The information is sent as parcels over the Internet. The information contained in the information packet is referred to as the payload. Furthermore, an information bundle contains critical steering information required to transport goods to a remote destination.
Privacy in a VPN
A VPN protects the private network by utilizing encryption and other security measures. It ensures that only allowed customers can connect to the network. The information cannot be denied. These networks provide a protected, encoded tunnel. This facilitates communication between far-away clients’ and friends’ networks.
The information sent between the two regions via an encoded tunnel cannot be read by another person. The system includes a few components for verifying both the external and private networks. This enables the remote user to connect.
Encryption and Security
Encryption is the process of encoding information. So only the PC with the appropriate decoder can read it. You can use encryption to secure email records. The information is sent to your computer, companions, or associates. An encryption key informs the PC about calculations. That is used to encode and decode information.
If you are highly occupied in finishing your accounting paper and have an online class to attend, when have a VPN service can approach an online service to attend it on your behalf and no one will know about it! You just need to say them Take my online accounting class for me and the job will be done quickly.
There are two most well-known types of encryption which are:
- Symmetric-key encryption and open-key encryption: All PCs (or clients) use a similar key. It is used for both encoding and decoding messages.
- Public-key encryption: Every PC (or client) has an open private key pair. A PC uses its private key to encode a message. Another PC utilizes the related open key to decode the message.
In a VPN, the PCs at each end of the passage encode the information that enters the passage. Then return it to the opposite end. Even yet, a VPN requires more than just a couple of connections to enable encryption. Here come the conferences. Webpage-to Website VPNs can use GRE or IPSec.
The GRE allows the system to wrap the passenger protocol for transit over the Internet Protocol (IP). This structure includes information about the types of packets you are sending. Furthermore, consider the connection between the sender and the collector.
Reliable delivery networks
To provide a specific level of protection to information transmitted via a VPN. It can be a mistake to focus solely on technical solutions. The truth is that if we focus on the primary goal. Then we may never attain it. The necessity for security stems from the need to securely share information over an open network. The client will utilize the VPN as a proxy because it is being used for personal reasons. Either to hide trade information or to circumvent security.
Practical approach
It has been discovered that several tactics can be employed to provide distinct types of protection for information. One can modify this information using the VPN. Concentrating just on technological difficulties might be quite problematic. If we focus on the important goal, we may never achieve it.
Security is required because information must be sent securely across an open network. The customer will use VPN as an intermediary to resolve specific difficulties. Need to conceal trade information or circumvent security.
These techs are always used to make VPN better every day and make students (as well as others’) life way easier when they have work to accomplish using the internet.
Read more: How to Ace an Effective Virtual Classroom Training Session?
Conclusion
VPNs are essential for students seeking to enhance their online education. VPNs can help students achieve their academic goals by overcoming geographical barriers, protecting their online activities, gaining access to online resources, increasing anonymity, and improving network efficiency. When choosing a VPN for educational purposes, consider dependability, security, server locations, and cost. A secure and continuous online learning experience is achievable with it.
AllAssignmentHelp – A Trusted Educational Partner in Assisting VPN for all Your Online Course Needs
We at allassignmenthelp are there all the time to sort your academic constraints. With our highly advanced and premium VPN-supported academic assistance service, we are very popular among high school and college students around the globe.
Take a quick look at some of our traits and services below:
- Online class help using premium VPN service
- Online exam help through premium VPN service
- Experts having deep knowledge about IP address masking and using VPN
- 24-hour availability
- Pocket-friendly costing
- Assignment writing facility for over 300 subjects
- More than 500 highly experienced and educated experts
Get the needed help from us when you require it the most.
Frequently Asked Questions
| Question 1: Are VPNs legal? Answer: Generally speaking using a VPN will not get you in any legal trouble, unless you are living in a country that has explicitly banned the technology. |
| Question 2: What are the uses of VPNs? Answer: Here are 5 ways to use a VPN: · Make public Wi-Fi more secure · Avoid targeted bandwidth throttling · Protect your right to privacy · Avoid price discrimination when shopping online · Access websites while traveling |